The Tor Browser Team is proud to announce the first stable release in the 4.5 series. This release is available from the
Download Tor Browser In Project page and also from our
distribution directory.
The 4.5 series provides significant usability, security, and privacy
enhancements over the 4.0 series. Because these changes are significant,
we will be delaying the automatic update of 4.0 users to the 4.5 series
for one week.
On the usability front, we've improved the application launch experience
for both Windows and Linux users. During install, Windows users are now
given the choice to add Tor Browser to the Start Menu/Applications
view, which should make it easier to find and launch. This choice is on
by default, but can be disabled, and only affects the creation of
shortcuts - the actual Tor Browser is still self-contained as a portable
app folder. On the Linux side, users now start Tor Browser through a
new wrapper that enables launching from the File Manager, the Desktop,
or the Applications menu. The same wrapper can also be used from the
command line.
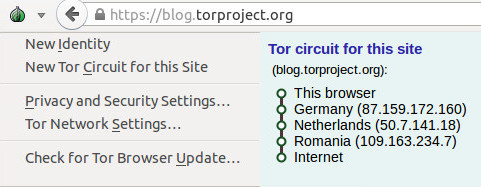
We've also simplified the Tor menu (the green onion) and the
associated configuration windows. The menu now provides information
about the current Tor Circuit in use for a page, and also provides an
option to request a new Tor Circuit for a site. Tor Browser is also much
better at handling Tor Circuits in general: while a site remains in
active use, all associated requests will continue to be performed over
the same Tor Circuit. This means that sites should no longer suddenly
change languages, behaviors, or log you out while you are using them.
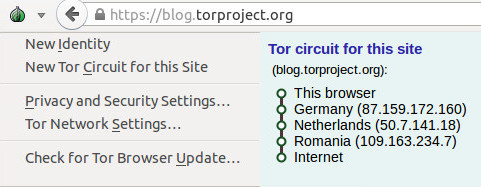
Figure 1: The new Tor Onion Menu
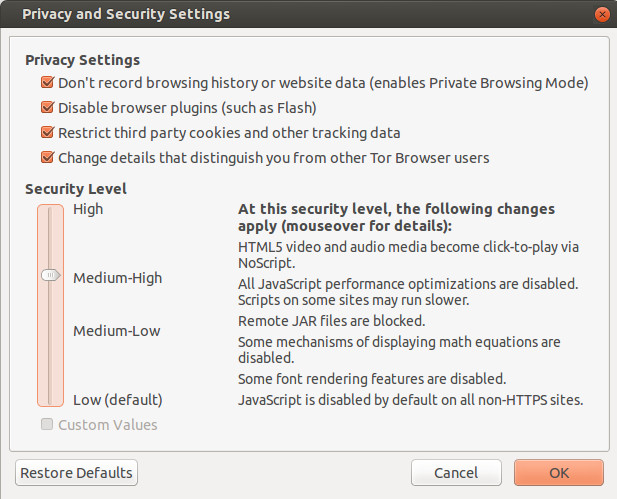
On the security front, the most exciting news is the new Security Slider. The Security Slider provides user-friendly
vulnerability surface reduction - as the security level is increased, browser features that were shown to have a high historical vulnerability count in the
iSec Partners hardening study are progressively disabled. This feature is available from the Tor onion menu's "Privacy and Security Settings" choice.
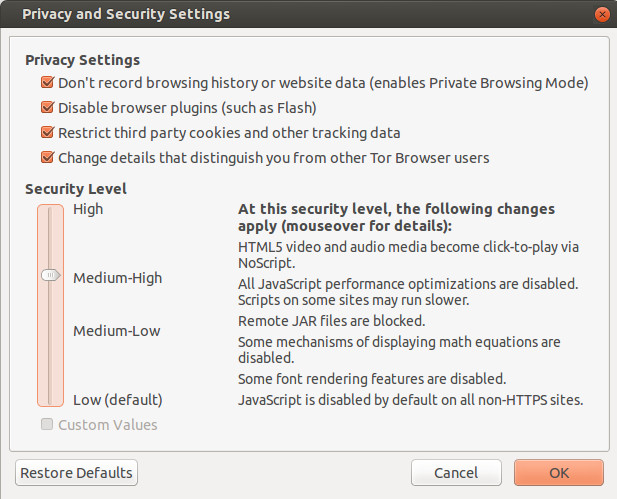
Figure 2: The new Security Slider
Our Windows packages are now signed with a hardware signing token graciously donated by
DigiCert.
This means that Windows users should no longer be prompted about Tor
Browser coming from an unknown source. Additionally, our automatic
updates are now individually signed with an offline signing key. In both
cases,
these signatures can be reproducibly removed, so that builders can continue to verify that the packages they produce match the official build binaries.
The 4.5 series also features a rewrite of the obfs2, obfs3, and ScrambleSuit transports in
GoLang,
as well as the introduction of the new obfs4 transport. The obfs4
transport provides additional DPI and probing resistance features which
prevent automated scanning for Tor bridges. As long as they are not
discovered via other mechanisms, fresh obfs4 bridge addresses will work
in China today. Additionally, barring new attacks, private obfs4
addresses should continue to work indefinitely.
On the privacy front, the 4.5 series improves on our pre-existing
first party isolation implementation to prevent third party tracking. First party isolation provides the property that third party advertisements,
like buttons,
and "mashup" content that is included on one site will only know about
your activity on that site, and will not be able to match it to your
activity while you are on any other site. In other words, with first
party isolation, Facebook, Twitter, and Google+ can't track you around
the entire web using their
infamous like buttons.
Specifically, in the 4.5 release, we now ensure that
blob: URIs are scoped to the URL bar domain that created them, and the
SharedWorker API
has been disabled to prevent cross-site and third party communication.
We also now make full use of Tor's circuit isolation to ensure that all
requests for any third party content included by a site travel down the
same Tor Circuit. This isolation also ensures that requests to the same
third party site actually use separate Tor Circuits when the URL bar
domain is different. This request isolation is enforced even when
long-lived "HTTP Keep-Alive" connections are used.
We have also improved our resolution and locale fingerprinting defenses, and we now disable the
device sensor and
video statistics APIs.
Our default search provider has also been changed to
Disconnect. Disconnect provides private Google search results to Tor users without Captchas or bans.
Here is the complete list of changes in the 4.5 series since 4.0:
- All Platforms
- Update Tor to 0.2.6.7 with additional patches:
- Bug 15482: Reset timestamp_dirty each time a SOCKSAuth circuit is used
- Update NoScript to 2.6.9.22
- Update HTTPS-Everywhere to 5.0.3
- Bug 15689: Resume building HTTPS-Everywhere from git tags
- Update meek to 0.17
- Include obfs4proxy 0.0.5
- Use obfs4proxy for obfs2, obfs3, obfs4, and ScrambleSuit bridges
- Pluggable Transport Dependency Updates:
- Bug 15265: Switch go.net repo to golang.org/x/net
- Bug 15448: Use golang 1.4.2 for meek and obs4proxy
- Update Tor Launcher to 0.2.7.4. Changes since 0.2.7.0.2 in 4.0.8:
- Bug 11879: Stop bootstrap if Cancel or Open Settings is clicked
- Bug 13271: Display Bridge Configuration wizard pane before Proxy pane
- Bug 13576: Don't strip "bridge" from the middle of bridge lines
- Bug 13983: Directory search path fix for Tor Messanger+TorBirdy
- Bug 14122: Hide logo if TOR_HIDE_BROWSER_LOGO set
- Bug 14336: Fix navigation button display issues on some wizard panes
- Bug 15657: Display the host:port of any connection faiures in bootstrap
- Bug 15704: Do not enable network if wizard is opened
- Update Torbutton to 1.9.2.2. Changes since 1.7.0.2 in 4.0.8:
- Bug 3455: Use SOCKS user+pass to isolate all requests from the same url domain
- Bug 5698: Use "Tor Browser" branding in "About Tor Browser" dialog
- Bug 7255: Warn users about maximizing windows
- Bug 8400: Prompt for restart if disk records are enabled/disabled.
- Bug 8641: Create browser UI to indicate current tab's Tor circuit IPs
- (Many Circuit UI issues were fixed during 4.5; see release changelogs for those).
- Bug 9387: Security Slider 1.0
- Include descriptions and tooltip hints for security levels
- Notify users that the security slider exists
- Make use of new SVG, jar, and MathML prefs
- Bug 9442: Add New Circuit button to Torbutton menu
- Bug 9906: Warn users before closing all windows and performing new identity.
- Bug 10216: Add a pref to disable the local tor control port test
- Bug 10280: Strings and pref for preventing plugin initialization.
- Bug 11175: Remove "About Torbutton" from onion menu.
- Bug 11236: Don't set omnibox order in Torbutton (to prevent translation)
- Bug 11449: Fix new identity error if NoScript is not enabled
- Bug 13019: Change locale spoofing pref to boolean
- Bug 13079: Option to skip control port verification
- Bug 13406: Stop directing users to download-easy.html.en on update
- Bug 13650: Clip initial window height to 1000px
- Bugs 13751+13900: Remove SafeCache cache isolation code in favor of C++ patch
- Bug 13766: Set a 10 minute circuit lifespan for non-content requests
- Bug 13835: Option to change default Tor Browser homepage
- Bug 13998: Handle changes in NoScript 2.6.9.8+
- Bug 14100: Option to hide NetworkSettings menuitem
- Bug 14392: Don't steal input focus in about:tor search box
- Bug 14429: Provide automatic window resizing, but disable for now
- Bug 14448: Restore Torbutton menu operation on non-English localizations
- Bug 14490: Use Disconnect search in about:tor search box
- Bug 14630: Hide Torbutton's proxy settings tab.
- Bug 14631: Improve profile access error msgs (strings for translation).
- Bugs 14632+15334: Display Cookie Protections only if disk records are enabled
- Bug 15085: Fix about:tor RTL text alignment problems
- Bug 15460: Ensure FTP urls use content-window circuit isolation
- Bug 15502: Wipe blob: URIs on New Identity
- Bug 15533: Restore default security level when restoring defaults
- Bug 15562: Bind SharedWorkers to thirdparty pref
- Bug 3455: Patch Firefox SOCKS and proxy filters to allow user+pass isolation
- Bug 4100: Raise HTTP Keep-Alive back to 115 second default
- Bug 5698: Fix branding in "About Torbrowser" window
- Bug 10280: Don't load any plugins into the address space by default
- Bug 11236: Fix omnibox order for non-English builds
- Also remove Amazon, eBay and bing; add Youtube and Twitter
- Bug 11955: Backport HTTPS Certificate Pinning patches from Firefox 32
- Bug 12430: Provide a preference to disable remote jar: urls
- Bugs 12827+15794: Create preference to disable SVG images (for security slider)
- Bug 13019: Prevent Javascript from leaking system locale
- Bug 13379: Sign our MAR update files
- Bug 13439: No canvas prompt for content callers
- Bug 13548: Create preference to disable MathML (for security slider)
- Bug 13586: Make meek use TLS session tickets (to look like stock Firefox).
- Bug 13684: Backport Mozilla bug #1066190 (pinning issue fixed in Firefox 33)
- Bug 13788: Fix broken meek in 4.5-alpha series
- Bug 13875: Spoof window.devicePixelRatio to avoid DPI fingerprinting
- Bug 13900: Remove 3rd party HTTP auth tokens via Firefox patch
- Bug 14392: Make about:tor hide itself from the URL bar
- Bug 14490: Make Disconnect the default omnibox search engine
- Bug 14631: Improve startup error messages for filesystem permissions issues
- Bugs 14716+13254: Fix issues with HTTP Auth usage and TLS connection info display
- Bug 14937: Hard-code meek and flashproxy node fingerprints
- Bug 15029: Don't prompt to include missing plugins
- Bug 15406: Only include addons in incremental updates if they actually update
- Bug 15411: Remove old (and unused) cacheDomain cache isolation mechanism
- Bug 15502: Isolate blob: URI scope to URL domain; block WebWorker access
- Bug 15562: Disable Javascript SharedWorkers due to third party tracking
- Bug 15757: Disable Mozilla video statistics API extensions
- Bug 15758: Disable Device Sensor APIs
- Linux
- Bug 12468: Only print/write log messages if launched with --debug
- Bug 13375: Create a hybrid GUI/desktop/shell launcher wrapper
- Bug 13717: Make sure we use the bash shell on Linux
- Bug 15672: Provide desktop app registration+unregistration for Linux
- Bug 15747: Improve start-tor-browser argument handling
- Windows
- Bug 3861: Begin signing Tor Browser for Windows the Windows way
- Bug 10761: Fix instances of shutdown crashes
- Bug 13169: Don't use /dev/random on Windows for SSP
- Bug 14688: Create shortcuts to desktop and start menu by default (optional)
- Bug 15201: Disable 'runas Administrator' codepaths in updater
- Bug 15539: Make installer exe signatures reproducibly removable
- Mac
- Bug 10138: Switch to 64bit builds for MacOS
Here is the list of changes since the last 4.5 alpha (4.5a5):
- All Platforms
- Update Tor to 0.2.6.7 with additional patches:
- Bug 15482: Reset timestamp_dirty each time a SOCKSAuth circuit is used
- Update NoScript to 2.6.9.22
- Update HTTPS-Everywhere to 5.0.3
- Bug 15689: Resume building HTTPS-Everywhere from git tags
- Update meek to 0.17
- Update obfs4proxy to 0.0.5
- Update Tor Launcher to 0.2.7.4
- Bug 15704: Do not enable network if wizard is opened
- Bug 11879: Stop bootstrap if Cancel or Open Settings is clicked
- Bug 13576: Don't strip "bridge" from the middle of bridge lines
- Bug 15657: Display the host:port of any connection faiures in bootstrap
- Update Torbutton to 1.9.2.2
- Bug 15562: Bind SharedWorkers to thirdparty pref
- Bug 15533: Restore default security level when restoring defaults
- Bug 15510: Close Tor Circuit UI control port connections on New Identity
- Bug 15472: Make node text black in circuit status UI
- Bug 15502: Wipe blob URIs on New Identity
- Bug 15795: Some security slider prefs do not trigger custom checkbox
- Bug 14429: Disable automatic window resizing for now
- Bug 4100: Raise HTTP Keep-Alive back to 115 second default
- Bug 13875: Spoof window.devicePixelRatio to avoid DPI fingerprinting
- Bug 15411: Remove old (and unused) cacheDomain cache isolation mechanism
- Bugs 14716+13254: Fix issues with HTTP Auth usage and TLS connection info display
- Bug 15502: Isolate blob URI scope to URL domain; block WebWorker access
- Bug 15794: Crash on some pages with SVG images if SVG is disabled
- Bug 15562: Disable Javascript SharedWorkers due to third party tracking
- Bug 15757: Disable Mozilla video statistics API extensions
- Bug 15758: Disable Device Sensor APIs
- Linux
- Bug 15747: Improve start-tor-browser argument handling
- Bug 15672: Provide desktop app registration+unregistration for Linux
- Windows
- Bug 15539: Make installer exe signatures reproducibly removable
- Bug 10761: Fix instances of shutdown crashes
Sumber : blog.torproject.org











![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEiFF0y4BFwOfqS36DSUSQ9AP5eRuPEnNbo1V1cnTNpdjU7LtE4h276bzd3aHYateT1-xaSX0mjWoJtvNa7gO6rexiYVad3PdJV-estLNRMpxkTGZwIxQSNO1bXzjy2DILzA0gtAp40Wn8PH/s1600/Gasper+Vladi.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEjnxCZAsAD1XRykMx0aG5bhzo5hBRpHPZyz-7tpcAv7IG3cUQ20dYtME7vJKqqamaak8BwjRaxydwoPftWNJK39PvLscy-FsyKHAv76hAFTeQgJ_6iNaC33EHXHGdwlFUHAq5HqcYFIzkfY/s1600/Pengisi+Suara+Gasper.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEhcDOgwada0vGVqIpbhWNgD_EGnMOuGmDpYJWFKnmSGIR2eUSiTzMDSGi3SQtT36Dqlct_OPfrLgrNVuTBAz4weQMFhn-r7cK00TMoz9venw6ui4LeJ5bsamm11gLsDoLRDNRQk1Jvm307u/s1600/Ayane+Sakura.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEjmhAeLlmSmkhF8yDJg7xdMg4ER-gEo3dyIFCj9huO1e7qBZcfbu6WtUvtSclL-z-DfRRnRKdcCodZxsPe6_Z3geXmgKKikS_ZSGgm17bEW2kynufgIZQZc56mWrFo9TLAF3G__OSnxuNf8/s1600/Pengisi+Suara+Anime+High+School+Dxd+03.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEh66upqWveQJfiaPBv2A2yNpJUK-oR7qEm7fLq6xygChkv19EifZF0d9mksQuna9XHRDHF2cSpQAwrbFIuZ579P4keN_sKWiZW7cDVRAxg2syQ0VnhtrImp9q_Tt8siJ_12wMM-bJ9vyz3G/s1600/Pengisi+Suara+Xenovia.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEgymwo3N9MgcEgx5jyUZL2K3VSgRIb7mm2bQkX7FJgqpCWvg_PFcTpo2WxF2SwHE0Ik43uLeCbgPq973jpb46Bin-YLrIej-HlZgffvbPPyttI9K9u2VX2_QQONkCbObvsQqMcip1d6YJhQ/s1600/Asia+Argento.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEiZXH0xH4gRuh9FVhamA4aePxWa0eGnunYNP3N6avySMKQ2-aFeVdgKyBmgUdYmk_EOZ4VJTYM9NDJModEys0lOWHiZVHnZTReEPPZahLcE7RIGJE6H6_aj9sRo_IwYgn2G_aRsjICzOfZ7/s1600/Pengisi+Suara+Asia+Argento.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEj59GA_KrUK6G8KReYrCEZAWGA0ZN9XA3cI2YGH5DBM5kJkwNDDnJ5A0JN-WZ8jxVG7X9x5NDt8JHFdTRPje6sjsTf6UMid8csSMZhg5vA4lFmcUqkN3GxCfhqaWA_prJ4cVjX75z0gR2hm/s1600/Pengisi+Suara+Azumi.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEgBbSUq8fVyq1LvEPWGAMaAghb78Ug4M7_5Vdi3X0Eug3OciOz8wA9kQTraw1l4XI2adW5iTNEhkHt79c4e59qh-GC2bbGcrzoMBapdtmTWDjkt6wiSxpt6DjC39oDpoRyP1UqU8RynvK1g/s1600/Kiba+Yuuto.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEi7YG9pGYxeudO-j6oCBkQtBjYwSejpwAxrar4fhgzVNHVxgbyivKv2Qa2xi0GNRsUGNEj2rU32GS5rhjZa4mI3cUMZcWgF5F4wcJoVsG3Mc4aF2Memf6CzgbuLv63HwHvA69RPgNxx_n5z/s1600/Pengisi+Suara+Kiba+Yuuto.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEilicIGhP2IXh5fIUKwwuymHsnfku97Vf3w_e2i8zrNvMUAo98kawgZqLksL5igBMInfsq16ObwtHCLFUgaQw8ySC5VlmEW9TlDI3eLoz3qHutTq7xIC12nCZg6O15IlGrAfJI3emNsQBsE/s1600/Kenji+Nojima.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEjVvilJrF5Z3XBAhchEaUvTu8YdWLCT9_fGqzj6pTu9prlqBJswfm1W9UjJF8l8pvjUeep2lGgwjeCbjRWHPawBiUi-Ed0c2gMYZsYiFSCzh2g4fAcfW23ZG7jvpcL0uio-FtdyXrfmmcgy/s1600/Pengisi+Suara+Anime+High+School+Dxd+04.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEi9QVQJOi9lDSFzEZZgXWoWvD-yx2u9jyWEJZ0z5UQUWTG6ybfZ4MMG0iRGg-8MX3S1N2T6Thj33yejPfmbYKC6HpdBTTvA49Pb8I-Bx-lNauxaGiEG366pT81hcUOt9cGe6LSHZQ4SfPMi/s1600/Pengisi+Suara+Koneko.jpeg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEiK-vpnD5177uhfAnV4qsEcI3-Uf2WUrvIQ-ImuAzRbU8tHDlw2jirHwljQAaNmp_XZfTH_Ua-zPVbh4_k2VLSKhLaZLYAQ4FO3wHFWjxmhoxUQU2lX38Mc8i2T9XE5ExkSQITwDKbFJKWW/s1600/Ayana.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEh3uTn_DF91u3GOc8W3ybQ74K9y8puI-AXR0qL2uIJZOfpHm89owLAJmYqA5hTyMTdChsduzCP00V8bMVTmnCDr8eT-ijhcFMlh2xymjsy9FXRAm01i3tMv9dxlrXYGroIpLarZyE8-HzuW/s1600/Pengisi+Suara+Anime+High+School+Dxd+02.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEi5WnVMTmP4AEYBLaWMFMhlY4JUZBMa1FcjBKQFIgFhihwfVP2UpM-9eamqJ3yJeDDRZs5A14Sao7Vy5W0CXUiA6dxvAGSQ8o5U7Rje8kQ8V5BONPKTNFyui0THX9ObZ-tIIgNp5P2qad77/s1600/Pengisi+Suara+Himejima+Akeno.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEhUGHdOvZQ_5vRWznunYsbk2bbUK1HxSmgN1pNnx3SukvVdo7aiIEvuxhi3KTkPBC3lz3TSBXao_TawYgloVHwo7KL5cj0Ijjozv1L3v7kwZbnWG1iyXJ6GJoZiuHMWoOAodSHFT_QHHmRa/s1600/Shijuka+itou.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEj_VdtFsqrd99YqLgi_LMUztogHvVaTrYTiiwC_fftZjKDgAUNxFzpGsDQiq1HIg_vj9qInsxiyb0l124leqF-gPPeeEY0O2uUUf3HHpByWW8EARUSFnaxDMDUkHWGZo2xTLuxslLdREOVe/s1600/Pengisi+Suara+Anime+High+School+Dxd+01.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEhd4oG0TH3f4Sx6mMQrZAZyqMNfbTaBpnAf_5LJdyf9WAb4TkxPeW4cfWvEUnMvzSNMIyb7BTaCrd1hGZE4PfGhkasajZbfIOQxDX70YOx-zIW3c8wxSB3kkRYDtmAJOVUSvKZucwYN4UVr/s1600/Pengisi+Suara+Rias+Gremory.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEjdnYLkkA3M-iJ-Z7NFfGiCucO-CWYmz9ZRSlrozGlDwQ9YrdY-Aqpqb1pPEwhWVHpf97Td-KbNV2kUoQTlUWu3E62iLhrxJyAc9Ybx7QPcBTmydrueYqYxIp5OReIdZ2EjHlqt2S-uqzwS/s1600/Yoko+Hikasa.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEhwMap2orOpWqyhHqpzqjOUH5SFmffIKLoEtZYImboBSlNgxoVN3jmUe1WzL73lJA7UYZNx0uYG-8DtNS4oEvldz1Dm6Sn3xaQuG3uB2PNv24TW6odx7qdt3GyylCjdmxtDR1b22fcYxmjJ/s1600/Hyoudou+Issei.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEi0ccJVM_-f_qYmf5A424BBOnT8tr-UkKAfx97mMENZK_KcSlXW2xqbBqrpmUSCsGUeyehhdDPqm_YY2Xc6nFaiEQ_P_g7EvoZ_Bpc-3pL6k-ydGmFPbtmrmOE7QLw_rIIfWT46PfQM97Hb/s1600/Pengisi+Suara+Hyoudou+Issei.jpg)
![[ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd [ Info-Anime ] Pengisi Suara Chara-Chara Di Anime Highschool Dxd](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEjCKrY0IXymHinoKIIV1aUKMG0O0Y3joo9R_pK8OcE0XZTbWBOPMFWoTCAqgT15HlGxmcOeD0hkbyuFTfVSajfdeb0qYZzB62k2PaF9GuTKzMYDc4cYjXnHnb1ErE-GbQ8AcoVI61vR5ZjO/s1600/Yuki+Kaji.jpg)